
Executive summary
On February 24, 2022, Avast Threat Research published a tweet announcing the discovery of new Golang ransomware, which they called HermeticRansom. This malware was found around the same time the HermeticWiper was found, and based on publicly available information from security community it was used in recent cyberattacks in Ukraine. The new ransomware was likely used as a smokescreen for the HermeticWiper attack due to its non-sophisticated style and poor implementation.
In this report, we present our analysis of HermeticRansom, which we also call Elections GoRansom.
Our findings in a nutshell:
- Elections GoRansom (aka HermeticRansom) was used to target assets on the same day as HermeticWiper;
- The developers used a sarcastic function-naming scheme related to US presidential elections;
- The malware does not use any kind of obfuscation and has pretty straightforward functionality, suggesting it was created in a short amount of time.
HermeticRansom’ technical analysis
The malware is created in Golang and uses no anti-analysis components as string encryption, function names stripping, etc. After execution, it creates an ID which is later used as the key from the array of Latin alphabet characters and numbers using a standard Golang rand function:
Then the malware identifies hard drives present on the infected system and collects a list of directories and files, excluding the Windows and Program Files folders.
After that, the ransomware note is created as a “read_me .html” file and dropped to the user’s Desktop folder. The note contains the victim ID and the actor’s contact emails on the ProtonMail domain; emails are hard-coded as seen below:
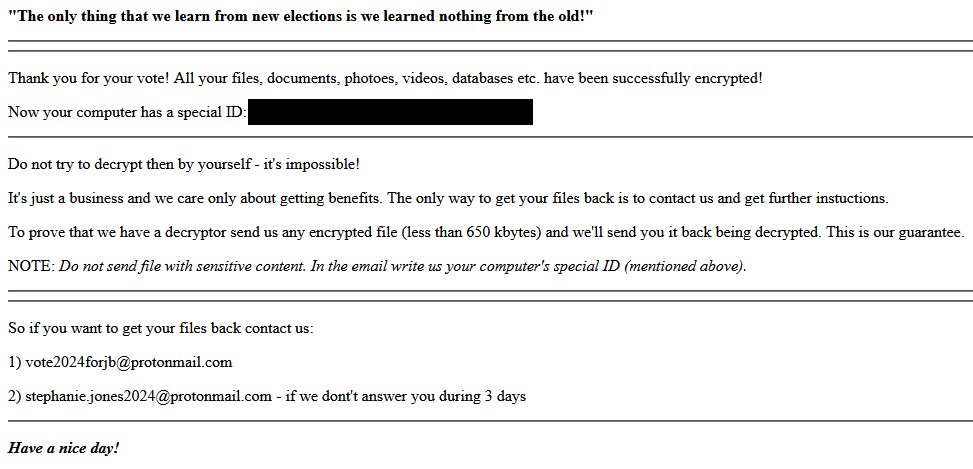
Ransomware note in HTML format
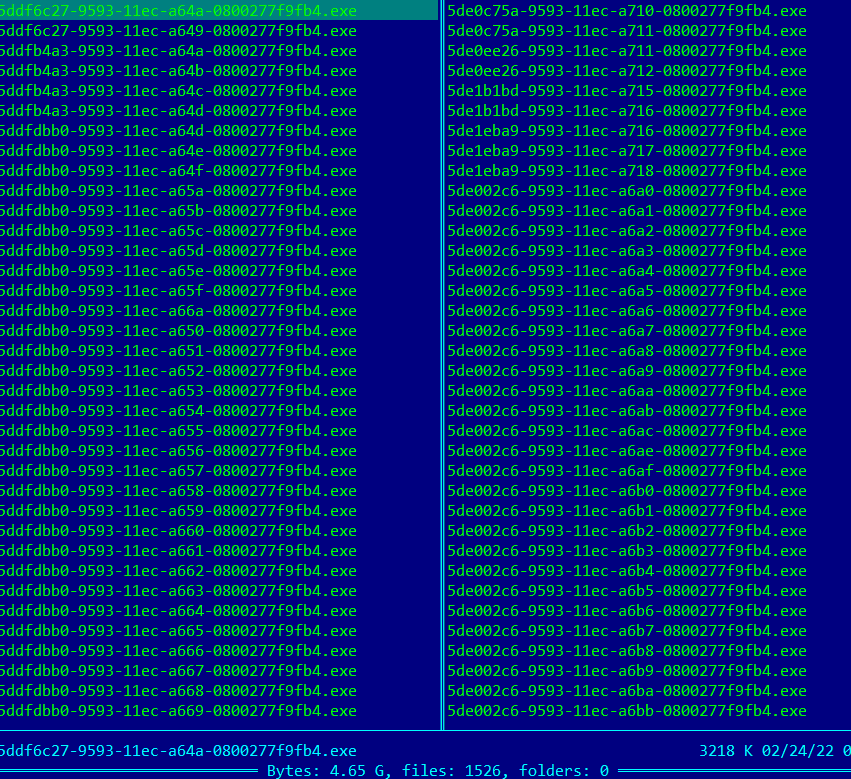
The malware utilizes a strange ineffective encryption workflow – it creates a copies of the initial sample and runs them as separate processes for each file encrypted; copy names are generated using Golang GUID library functions.
Self-copies made by HermeticRansom
To encrypt victims’ data, HermeticRansom relies on a list of hard-coded files types, as follows:
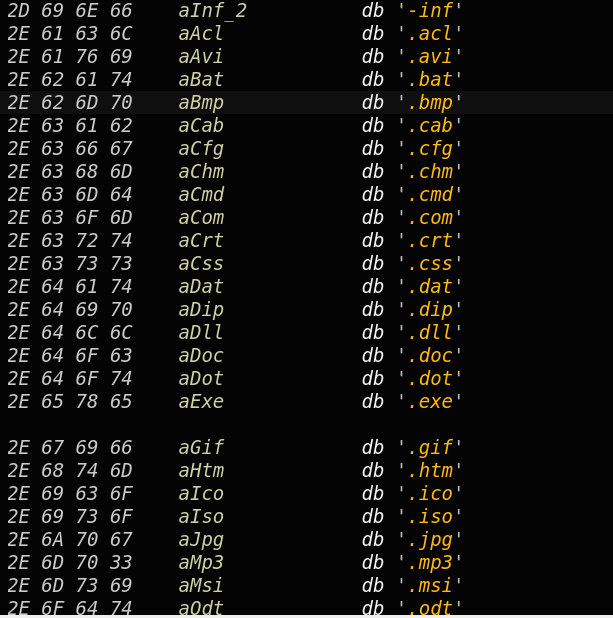
List of hardcoded file extensions to encrypt
Files are encrypted using the AES algorithm with the generated key. Then the AES key is encrypted with RSA-OAEP. OAEP is parameterized with a hash function that is used as a random oracle. The hashing function is SHA-256. The RSA public key is hard-coded as a base64 blob. After decoding the key in JSON format, it is converted to a byte array:
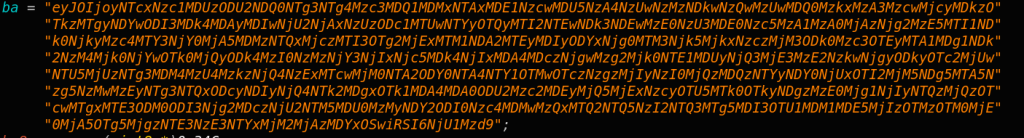
Hardcoded encryption public key
Once files are encrypted, HermeticRansom appends a “.encryptedJB” extension to each. Also the ProtonMail email address is appended to the filename:
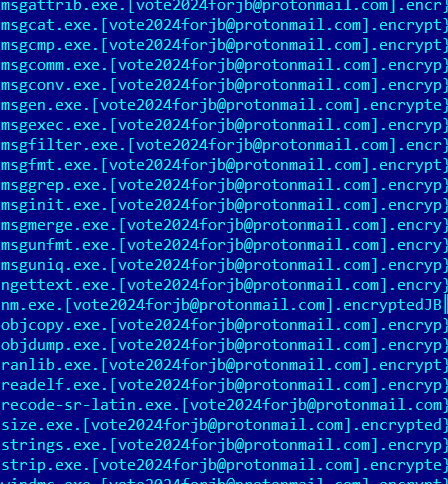
Encrypted files with the new extension
The malware structures and methods are named in a sarcastic manner related to US presidential elections.
HermeticRansom’ attribution
Given the circumstances under which HermeticRansom appeared, including the date, time and victims’ geo-locations, we have moderate confidence it is connected with HermeticWiper’s general objectives – destroying or otherwise making Windows systems unusable due to data loss.
Conclusions
HermeticRansom is an excellent example of a targeted attack preventing victims from using their data while also potentially acting as a smokescreen for further attacks. The simplicity of the code, along with the grammar and spelling errors left in the ransom note, probably indicate that it was a last-minute operation, potentially deployed to boost the effectiveness of other cyber-attacks on Ukraine.
Indicators of compromise
HermeticRansom MD5
d5d2c4ac6c724cd63b69ca054713e278
Elections GoRansom – a smoke screen for the HermeticWiper attack






















Andrew
Hello, the extension in the screenshot is .[vote2024forjb@protonmail.com].encryptedJB – that is, with .encryptedJB at the end